Kickass Websites
Our web design services are focused on more than just making your new site look pretty. Building a conversion-friendly website is an integral part of your online marketing strategy as a whole. It’s how you get users to your website and turn them into qualified leads.
Design Philosophy
Web Design Services for Small Business
Our philosophy is centered around the user’s needs: Simple. Clean. Uncluttered. If your visitors can’t find their way around your website, they’re not going to stick around for long. Our job is to make sure they do. At Frahm Digital, beauty and function go hand in hand.
GET IN TOUCH

We Do Design
SEO WEB DESIGN
Solid search engine optimization practices like technical markup, formatting, and keyword-rich content keep your website at the top of Google.
MOBILE WEBSITES
The majority of traffic has shifted to mobile devices. We build websites that are mobile-first, to engage visitors on smartphones, phablets, tablets, laptops and desktops.
BLOG DESIGN
Fresh content attracts more organic traffic. With easy-to-use websites, it’s simple to add new content to your website and increase engagement among your target.
An SEO Web Design Company,
Here to Help

How Our Web Designers Do It
The team members at our web design company understand the importance of generating business through your website. By utilizing eye tracking and usability studies, search engine optimization best practices, and the latest design trends, we are able to build a website that attracts more leads and sales for your business and reflects the quality of your company’s brand.
Our group of web designers are trained in web design best practices and have an expert eye for UX improvements. If you’re looking for fresh ideas, all you have to do is ask. We’ll go over the numbers and get you an answer.
If you operate on a WordPress website design, you can easily update your site without any programming experience. We strive to save you more money by implementing easy tools that you and your employees can easily grasp.


About Frahm Digital: A Minneapolis Web Design Company
Frahm Digital is owned and operated by Mike Frahm. Officially founded in 2017, our company was born out of a growing freelance model that’s been Mike’s passion project for nearly a decade. While Mike cut his teeth at award-winning digital marketing and communication agencies in Minneapolis, he was simultaneously focused on winning new clients and providing a unique “creatively technical” approach to SEO.
Today, our company has served over dozens of clients around the U.S. with premier SEO services that get results. But don’t take it from us – take a look at what some of our clients have to say about our approach:
“Mike has helped with both print and digital asset production for our non-profit Community Driven/Cheap Laughs for Charity. He supplied key art direction when it came to the development of both our craft beer magazine and the supplemental website.”
– Craig Drehmel, CFO Community Driven
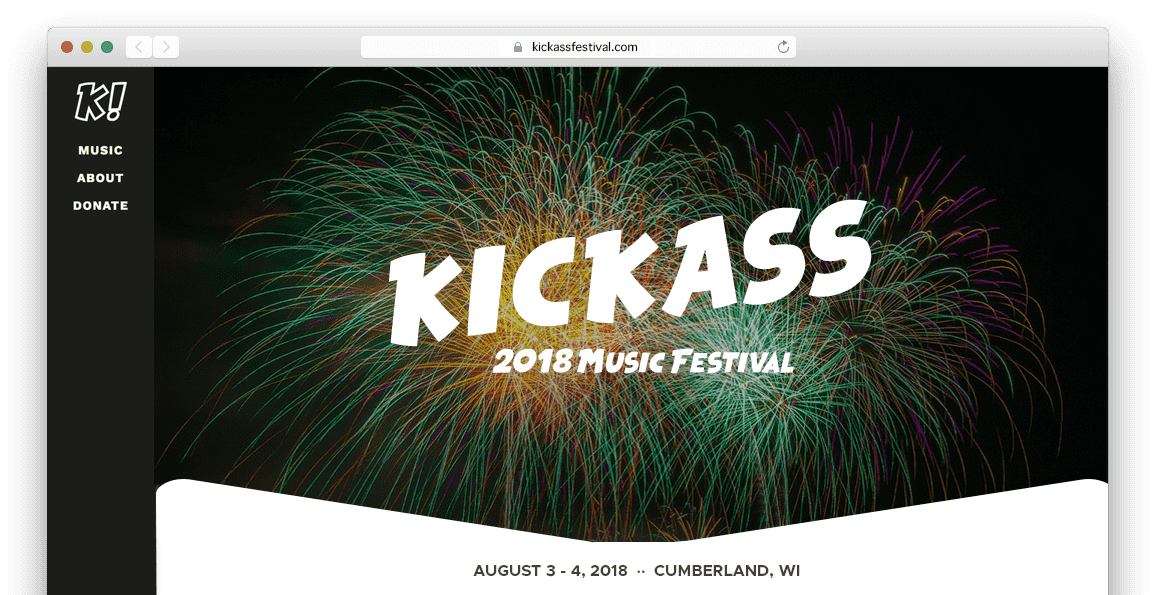
“Mike rocked the website he created for a special event I have every year. I really didn’t want to bother with it. He completely took ownership and exceeded any expectations I had with his creativity and execution. He was very open to any small adjustments and always took it a step further. Great person to work with! Highly recommend!”
– Steve Norwick, Owner SJN Sound
 More 5-Star Google Reviews >>
More 5-Star Google Reviews >>
While Frahm Digital is run by Mike, to stay lean and provide the client with lower costs, he occasionally enlists members of a personal network of highly skilled SEO professionals, technical writers, PR pros and marketing gurus in Minneapolis when the project calls for it. We’ll always take a personalized approach to each company we work with because your success is our success.
Find out more about our Minneapolis Website Design Company
Our Web Design Process
Our web design process is designed to enhance your brand online. We build beautiful, easy-to-use, search-friendly websites that let you take control of your web presence.
Educate
The first step in our web design process is to educate ourselves – on every piece of information pertinent to your brand, no matter how seemingly miniscule. We take the time to understand everything from the nuances of the market you serve to your ideal customer profile to the specific devices they’re using (and much, much more). There’s no such thing as a boring business, and we intend to find out everything there is to know to create a compelling brand story so we can show it off in creative ways.
We listen to your needs, desires and pain points and develop an accurate scope of your project. By working with you, our team can better understand what it is you’re trying to achieve by employing a web design company. When we partner up, we can cover much more mileage in a fraction of the time. Together, we can improve your web presence and build a compelling visual aesthetic online.Ideate
After we learn about your brand, audience, competitors and market, conducting website audits and what-not, we throw our compasses overboard and freestyle. We develop our initial ideas and identify unique solutions to complex web design problems. With our imaginations guiding us through ideation, there’s nothing we can’t dream up.
We like to adventure into the unknown; the unexplored, learning more and more about opportunities that exist for your brand online. There’s no stone left unturned when we’re on the case – we hunt for pieces of the puzzle and figure out how they fit into the larger, visual picture. When all the pieces fall into place, it’s time to move into website planning.Plan
A cookie-cutter approach – while delicious-sounding – isn’t the way we work. Once we’ve come up with a broad range of ideas, we trim down the fat and layout a website implementation plan. Our fully customizable website designs are centered around your goals as a developing or established brand. Whether you need quick WordPress consulting, graphic design or an entire website overhaul, we’ll help you take control of your web presence.
We also build our website with the highest search standards at the forefront of our strategy. Web design, combined with an actionable SEO strategy will improve your website’s performance from day one. Developing our SEO plan in conjunction with a new website ensures that your performance online will never be hindered.Execute
Our execution phase is where we bring your website vision to life. Our team works tirelessly to build a beautiful, functional, search-friendly website that you can update yourself. Whether you want to add content to the homepage, post a blog or upload a video, our websites are built with an easy-to-use backend that anyone with computer knowledge can figure out how to use.
When our plan is in motion, we must learn from our successes and failures, as any good leader does. If we don’t know how we’re performing, we can miss valuable design, conversion or promotional opportunities. We configure data analysis systems with your website so we can track the effectiveness of our web design – data-driven insights are key to any successful website. With a dedication to continual improvement, we adjust our scope as our data dictates.
